To keep pace with the rising demands of operating in an increasingly complex business environment, utilities are turning to external suppliers as never before. They’re looking for help with tasks ranging from the relatively mundane (such as vegetation management and the handling of customer calls) to the complex (including the facilitation of distributed power generation and the execution of large infrastructure projects). While the benefits of leveraging supplier capabilities are clear, the risks—including cyber, reputational, financial, legal, and regulatory ones—generated for utilities are potentially vast. The practice can also unwittingly thrust utilities into the headlines, as illustrated by the recent, rather unflattering press coverage of a number of high-profile incidents in which utilities’ suppliers played a prominent role.
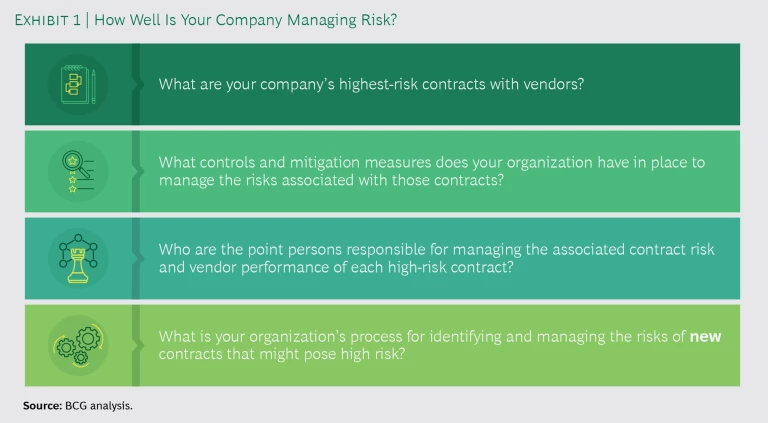
Fortunately, the risks associated with the use of suppliers can, in fact, be identified and mitigated. (See Exhibit 1.) But that requires taking a comprehensive, well-constructed approach—one that few utilities, in our observation, currently employ. Reasons vary for the absence of such an approach to supplier risk management among many utilities, including the complexities of program design and difficulties securing organizational buy-in for the needed investment.
But BCG has created an effective approach that can substantially reduce your chances of being blindsided by a major supplier-related event and enhance the strength and quality of your organization’s response if an incident does occur. It is tested, can be melded into your day-to-day operations relatively quickly, and can translate into tangible results almost immediately. What’s more, implementing it can produce broad benefits—including a more risk-cognizant culture and simplified, more automated procurement and supplier-management processes—within your organization.
Suppliers and Risk
The business and operating backdrop for utilities is becoming ever more complex. Utilities are expected to execute their day-to-day functions flawlessly, 24-7, amid tightening regulatory and safety standards and a general rise in customer expectations—all while keeping costs in check.
Simultaneously, utilities are expected to plan, manage, and execute major capital projects; adroitly navigate a rapidly evolving technological environment replete with smart meters, renewable energy sources, and other potentially game-changing developments; and keep investors and regulators happy. In addition, utilities must keep all of these balls aloft under close scrutiny, where the slightest miscue can be surfaced quickly and broadcast far and wide through social media.
Given this sweeping range of demands—and the associated breadth of expertise, skills, and work capacity necessary to meet them—it is hardly surprising that utilities are turning to suppliers more and more. Indeed, for many utilities, contracted labor now accounts for more than half of their total labor hours and for spending that is equivalent to as much as half of the utility’s revenues: many large utilities now spend multiple billions of dollars each year on suppliers.
Many large utilities now spend multiple billions of dollars each year on suppliers, amplifying traditional risks.
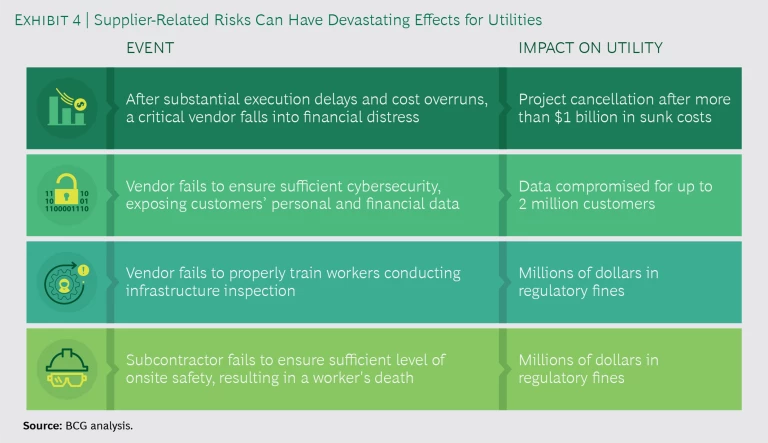
This growing reliance on outside parties amplifies the traditional risks that utilities face, such as the following:
- Cyber. The supplier’s security protocols might be more lax than the utility’s, unduly exposing the utility’s systems and customer data to hackers. (See “Supplier-Driven Cyber Risk: A Growing Threat That Could Be Very Costly.”)
- Operational. The supplier fails to follow established health and safety standards, resulting in injury or death.
- Reputational. The utility is held implicitly accountable by the media and public for errors committed by its suppliers.
Greater utilization of suppliers introduces new types of risk to utilities as well. Among these are the following:
- Fourth Party. The supplier engages subcontractors that the utility has not vetted.
- Contractual. The utility is prevented by contract restrictions from effectively monitoring the supplier’s work.
- Concentration. The utility becomes too dependent on a single contractor and either loses internal expertise and negotiating leverage or sees upward price pressure or deteriorating performance.
- Financial Distress. The contractor experiences severe financial difficulties and is unable to deliver the contracted services.
What’s more, the logistics of utilities’ business—including the need for 24-7 operations and accessibility for customers—make it difficult for utilities to reduce these risks through tighter supplier management. Utilities’ domains often span hundreds of miles, which makes the tracking of suppliers problematic.
A utility’s service area can also fall under the jurisdiction of multiple regulatory bodies, resulting in varying requirements for suppliers depending on location and exacerbating the challenge of monitoring and control. Contractor-reliant plants or facilities that need to operate around the clock (or at odd hours) pose similar practical hurdles, as does the sheer number (often hundreds) of contractors a utility may need to employ. The bottom line is that, even with the best of intentions, a utility can find it quite hard, if not impossible, to keep a sufficiently close watch and tight rein on its suppliers.
A Rigorous Approach to Supplier Risk Management
Some utilities have instituted formal programs to try to contain supplier risk, but we have noticed that many of these efforts fall short on at least one level. Some have an incomplete focus, concentrating on only a few specific kinds of risk or parts of the business. Others are backward looking, measuring only suppliers’ past performance or lagging indicators and offering no visibility into the likelihood of future problems. Still others fail to formally track supplier compliance with utilities’ or regulators’ guidelines or are siloed when a business unit fails to share information about a poorly performing supplier with others. And then there are those that misalign the probability or potential consequences of a given risk with their efforts to mitigate it.
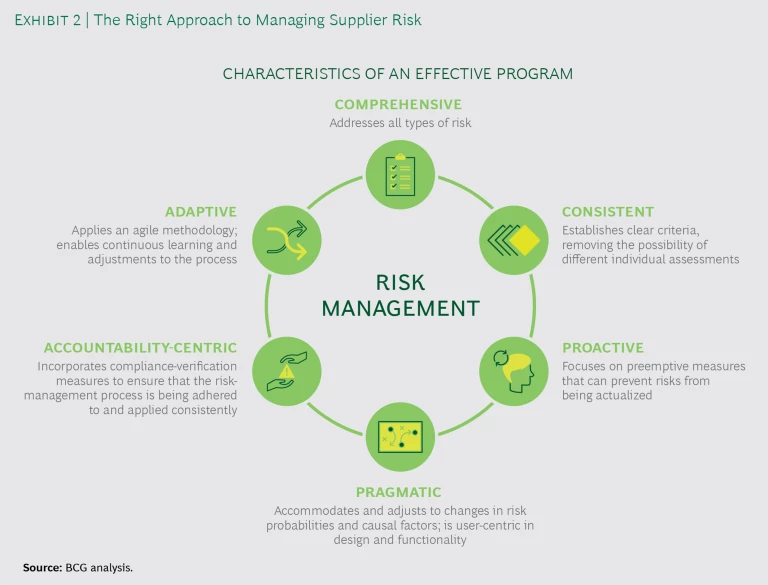
An effective supplier risk management program, in contrast, will have six attributes. (See Exhibit 2.)
It will:
- Be comprehensive, addressing all types of risk
- Forge a consistent interpretation of risk, establishing clear criteria so that the potential for varying individual assessments is eliminated
- Emphasize proactivity, focusing on the definition of preemptive measures that can prevent potential risks from being actualized
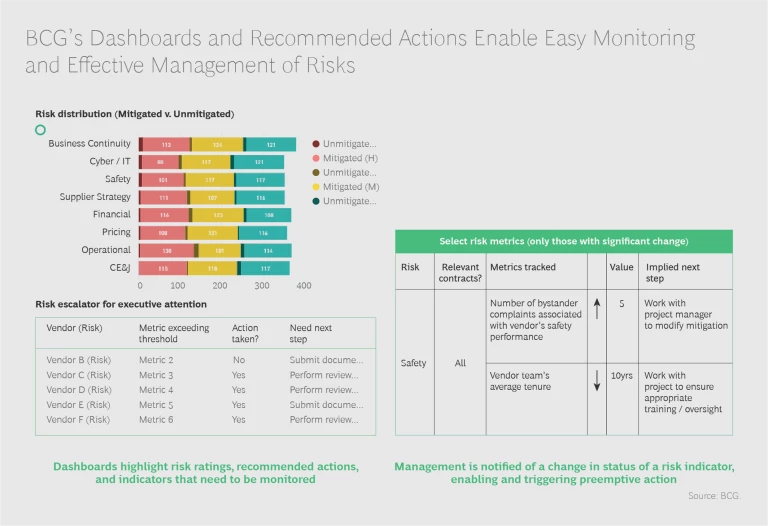
- Be pragmatic, accommodating and adjusting to changes in risk probabilities and causal factors, as well as user-centric in design and functionality (placing heavy emphasis on dashboards and other visual elements), especially from a contract manager’s perspective
- Establish accountability, incorporating compliance verification measures to ensure that the risk management process is being adhered to and applied consistently
- Be adaptive, applying an agile methodology and enabling continuous learning and adjustments to the process
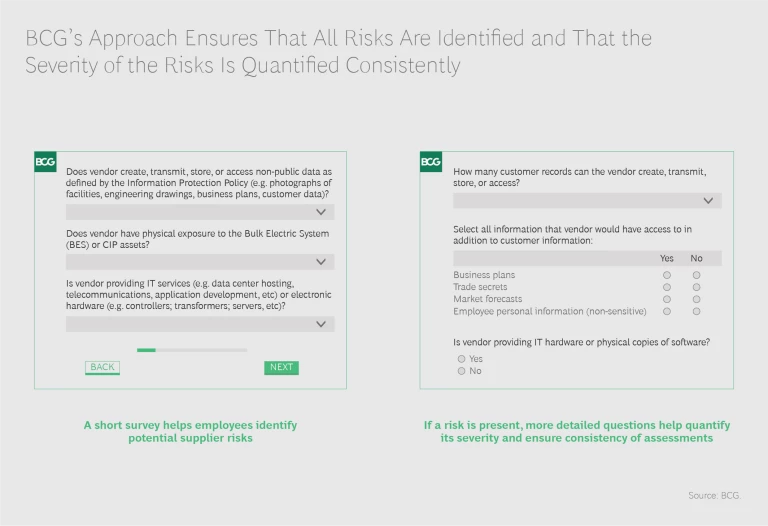
BCG’s approach to supplier risk management has all of these attributes. It is based on gaining a thorough understanding of each supplier and its particular mandate with a utility, and it’s grounded in a four-step process: identify, quantify, mitigate, and monitor. (See Exhibit 3.)
The process ensures that all relevant risks are surfaced; that risks are graded according to severity so that management knows where to concentrate its time, energy, and resources; that steps to mitigate risks are identified and shared with the appropriate people at both the utility and the supplier; and that the risks are sufficiently monitored at the management level by both the utility and the supplier. No stone is left unturned, no base is left uncovered. Simultaneously, the program accomplishes its goals without either interfering with the company’s ability to run its core business or demanding too much time from people.
Implementing such a program requires a multipronged approach. Leaders must commit to the program and make their commitment visible on an enterprise-wide basis: if leadership doesn’t lead, then the business and functional units are unlikely to follow. The business and functional units, in turn, must work in close collaboration with the supply chain and procurement functions. The enabling technology that underpins the dashboards and other visual elements necessary to make the program operate at scale must be designed, launched, and supported by training. A change management campaign, designed to get broad buy-in across the organization for the new approach to risk mitigation, must be undertaken. And the program’s phase-in must be user-centric, with particular attention paid to the needs of contract managers.
Successful implementation can greatly reduce the number of negative supplier-related incidents.
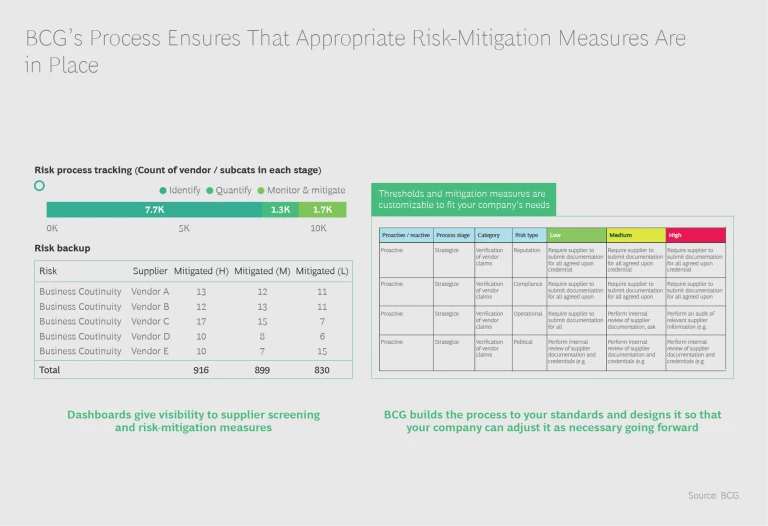
Admittedly, successful implementation isn’t easy. But the potential rewards for getting it right are sizable. Most visibly, the number of negative supplier-related incidents can be greatly reduced. This can spare the utility potentially large regulatory fines and costs associated with undoing or compensating for any damage caused by suppliers. (See Exhibit 4.) It can also strengthen the utility’s relationship with regulators and improve internal morale. In addition, time and resources that would have been devoted to managing supplier-driven crises can be dedicated to more productive activities. And the demonstration of control over supplier risk can foster broad cultural benefits across the organization, including a generally elevated focus on risk and risk mitigation.
Conversely, the downside of unsuccessfully implementing the program, or deciding to refrain from even trying to tackle supplier risk in a concerted manner, can be enormous. The number of negative supplier-related incidents could climb, leading to escalating fines and costs. The degree of regulator scrutiny could rise and remain elevated for an extended period. The utility’s reputation could suffer; customer attrition could surge.
In short, we think that, for most utilities, this is worth doing and doing well. We can help.
Why BCG?
BCG brings a wealth of relevant experience and capabilities to the table. We have worked with major energy companies, including a large utility, on managing third-party risk and have extensive risk management experience across industries. (BCG has worked with more than 50 companies on projects related to third-party risk in the past two years and has more than 20 risk experts in North America alone.)
We have substantial general experience with utilities, having worked on more than 1,800 projects in the past five years. We have a seasoned team of more than 300 experts devoted specifically to the power and utilities space as well as a depth of experience across the entire energy value chain. We have developed market-leading proprietary databases, benchmarks, and market models.
BCG can guide and assist in all aspects of implementation, from launching pilots to facilitating cultural change.
We can work quickly, efficiently, iteratively, and in close collaboration with you, using agile tools and methodologies and employing a “training by doing” approach with your teams. We can move rapidly from assessing your current risk management approach to designing a more optimized custom program, if necessary—one that is truly individualized and specific to your needs. We can guide and assist in all aspects of implementation, from launching pilots with a subset of suppliers to facilitating cultural change so that the program becomes part of your organization’s DNA. Throughout the process, we will challenge you and expect you to challenge us; together, we will arrive at a solution that meets your specific needs.
If you are interested in learning more about our approach to managing supplier risk and what we think BCG could do for you, we would love to hear from you.