Newton’s laws of motion serve as a suitable reference to today’s security landscape.
Contrary to popular belief, an organization’s IT security isn’t a setting that comes switched on by default. Actions need to be taken before an organization can claim that its business is secure. Of course, the corollary to this is that even though an organization might have policies, procedures and technology in place for it to consider itself secure, that state will only last as long as they aren’t degraded by external forces.
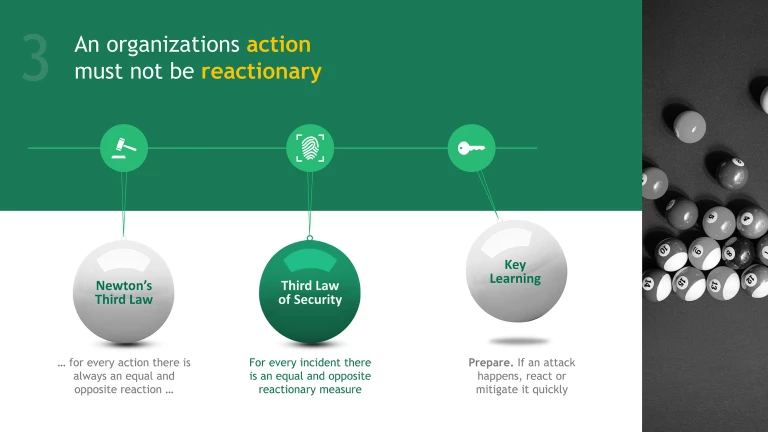
This picture has interesting parallels with Newton’s laws of motion, which have formed the bedrock of classical mechanics since they were first stated by the famed scientist in the late 17th century and led scientists to an awakening in the way that we understand the world and progress through it.
The first law of motion states that an object will remain at rest or in continuous motion (inertia) until acted upon by another force. The second law states that if acted upon by said force, the rate of change of its momentum will equal the size of the force. And lastly, the third law states that all actions will have equal and opposite reactions.
Organizations can gain a valuable perspective from the story contained in these three simple statements. Like anything with mass, they too will remain at inertia, or in an insecure state, until they are attacked. To have adequate security they need to adopt a speed of change equal to perceived threats. This is because for every incident an equal and opposite reactionary measure will be required to mitigate it.
To secure an organization, security must be created and maintained – some effort will always be required to continually update, maintain and adjust security processes in order to counteract the negative influence of external forces. But once the main thrust of security has been achieved, adjusting and upgrading existing security is much easier than to try and build it from scratch.
There is one more parallel that begs to be drawn from Newton’s law of gravitation: that every particle attracts another with a force proportional to the product of their masses inversely proportional to the distance between them. Putting mathematics aside to express the situation more simply, a large organization can expect to attract threats in line with its size, especially if it is already particularly vulnerable to them.
What this tells us that there is a relationship between resources, the speed at which your organization alters its state of security and the size of the organization itself. If you’re a medium- to large-sized organization attempting to create change in your organization’s existing state of security, or if are reacting to political or environmental threats, you will need either more time or more resources to implement adequate security.
The majority of organizations that attempt to drive changes out of a reaction to an incident yield little in the way of long-term security benefits. Organizations and their decision-makers who have already dealt with such incidents need to ask themselves some tough questions: Was the incident predictable? Was there no way to have pondered the possibility of this type of incident in the past? Could policies or procedures to mitigate the damage have been implemented if the budget, resources, or time to implement them existed before the incident?
Security (or bad security) is, more often than not, a series of reactionary measures put into place by organizations that do not take time to develop a holistic security solution which incorporates measures of risk and reward. Typically, this is the result of someone in an organizational ‘food-chain’ under heat from someone else above them. This heat trickles downhill until someone makes something happen only to be make it seem as if action is being taken, regardless of the effectiveness of that action. This creates the perception of a uniform level of security protection for the organization, and routine maintenance provides the further appearance of adequate provisions being taken to overcome the negative influence of outside forces.
Security measures that need to be implemented in haste will always consume more resources than proactive, rational and thought-out security measures that are implemented over time. Analyze your risk scenarios and implement measures to mitigate risks before they manifest – and make sure to allot plenty of time to doing so.
If organizations plan ahead, work to mitigate risks before they occur, and provide training and awareness of security measures and policies, they can reduce the negative impact that hasty reactions can have. It is impossible to eliminate reactionary thinking entirely, but rather than allowing reflexive decision-making to dictate their course, organizations should use them to strengthen their position by implementing policies and procedures that improve security processes for the long-term.