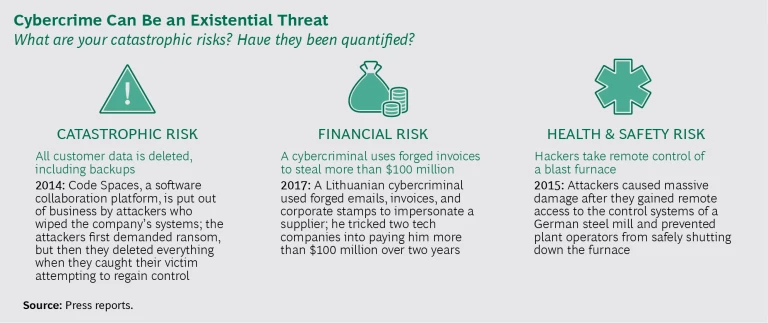
Most companies survive most cyberattacks. For example, two American tech companies lost more than $100 million to a crafty cybercriminal using forged credentials, but this financial attack never threatened the existence of the two businesses. A German steel mill lost control of a blast furnace—and the ability to protect workers—to hackers who gained remote access and overrode safety controls, but again, this company survived too.
Companies must take steps to address many types of risk—financial, operational, reputational, and others. But as business becomes ever more reliant on technology, addressing catastrophic risk—losing all data, production systems, or intellectual property—must also be on every executive’s agenda.
When hackers targeted Code Spaces, a software collaboration platform, they deleted all of the company’s data and its backups. Overnight, Code Spaces shut down. Existential threats are not always sudden, however. Over the course of ten years, hackers siphoned the intellectual property of a North American telecommunications giant: Nortel Networks. Nortel no longer exists, and although it has not been proven in court, many speculate that its stolen IP helped the company’s foreign rivals get a competitive edge.
The attacks on Code Spaces and Nortel show the kind of damage that dedicated hackers can cause when focused on a specific target. This summer, WannaCry and NotPetya demonstrated that even relatively unsophisticated, untargeted attacks can cause considerable, widespread damage simply because minimum defense mechanisms, such as well-executed patch management strategies, were not universally in place. Although a failure in patch management may sound like technobabble for the IT department to sort out, it is not a challenge that can be solved solely by using the most sophisticated technology or by employing the most talented IT and security professionals.
Making an organization cyberresilient requires close cooperation between business and technology leaders. Has your organization identified its digital crown jewels—the data, systems, or intellectual property that must be guarded most closely? This question must be answered before the IT teams can adequately prioritize what to patch. Likewise, has your organization calculated how much cyberrisk it can afford? If not, the IT and security teams are working in the dark.
Many companies fell victim to WannaCry and NotPetya because business leaders were inadequately trained about the risks posed by unpatched systems. These business leaders did not prioritize software maintenance, and their systems remained unpatched many months after the threat was known to security teams. Does your organization have a culture where business leaders work with security leaders to balance operational and security objectives?
Effective cybersecurity must be aligned with your business strategy, and cyberrisk must be an integral part of your corporate risk management strategy. (See Cybersecurity Meets IT Risk Management: A Corporate Immune and Defense System.) This cyberrisk strategy must be guided by an engaged board of directors. (See Advancing Cyber Resilience: Principles and Tools for Boards.) And the strategy must be implemented and managed by executives that understand the risks. (See “Building a Cyberresilient Organization.”)
Does your company have a well-formed cybersecurity strategy? If your organization’s existence depended on it, could executives answer the following questions?
Risk Management
- What is our most critical data, and who can access it? What are our most critical assets?
- How much cyberrisk, physical risk, and brand risk can we afford?
- How do we address vendor, partner, and ecosystem risk? How do we gain consumer trust?
Governance, Policies, and Processes
- Who owns cybersecurity and cyberrisk in our organization, and how are they supported?
- How have cybersecurity and cyberrisk management processes and policies been deployed?
- When did we last test our network and our incident response process by asking “what if…”?
External Participation and Internal Collaboration
- Are we competing with our rivals on cybersecurity or collaborating with them?
- Are our cybersecurity, safety, and quality management functions working together?
Cybersecurity Culture
- Have we established an appropriate cyberrisk culture in our organization?
- How do we use our cybersecurity culture to enable our business and digital strategies?
If you don’t know the answers, it is time to get to work.
This article was originally published by CBI.